Sensitive Data Analytics, Without Sacrificing Data Privacy
Address the compliance and security concerns associated with analyzing sensitive data – all while achieving zero-touch workflow execution through integrations.
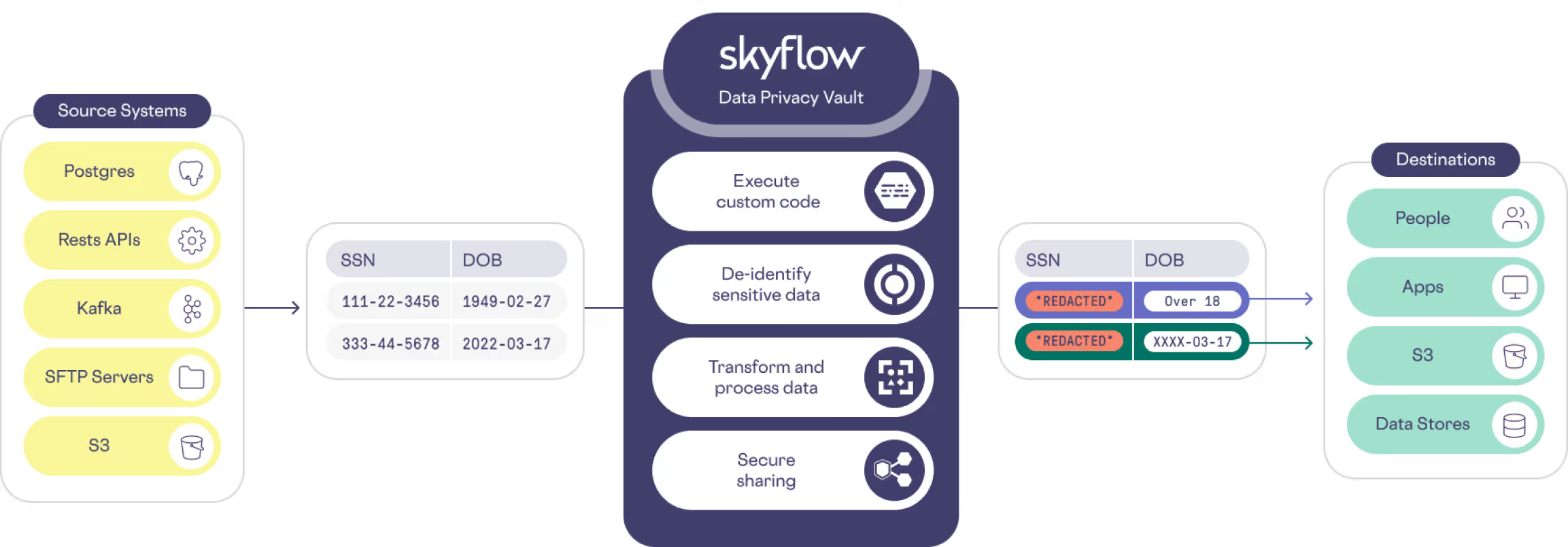
How Skyflow Helps
Skyflow lets you de-identify sensitive data so you can keep it out of your data analytics pipelines without sacrificing data utility for analytics. De-scope your data warehouse and data lakes from the responsibilities of data privacy, data security, and compliance.
Why Skyflow
Skyflow helps you de-identify sensitive data during your ETL process, replacing sensitive customer data with non-sensitive tokens so you can maximize utility for analytics while minimizing risks. Manage sensitive data using the same approach that innovators such as Apple and Netflix use – a zero trust data privacy vault.
Reduce Your Privacy, Security, and Compliance Risk
Reduce your privacy, security, and compliance risk – replace sensitive data with deterministic tokens, so youcan safely use tokens in your data analytics pipelines without compromising on key use cases or impeding critical analytics workloads.
Always Encrypted Data Analysis
Query sensitive customer data while keeping it safe and secure – build machine learning models, analyze customer behavior, or build secure data triggers. Decide how sensitive data is displayed to authorized users and workflows by choosing to hide part of it, show all of it, or completely remove it.
Process and Analyze Sensitive Data
Process and analyze sensitive data easily and safely without the need for additional development or compliance work. Skyflow empowers you to extract, protect, and process sensitive data using custom code, giving you the flexibility to handle data in the way that best suits your needs.